I see a pattern in early-stage companies that is easy to miss because it looks like maturity. Teams borrow processes that work later, when an organization is larger and roles are more specialized, and they apply them far too early.
Shashwat Sehgal
Latest research and insights
The day “access” stopped meaning “login” and started meaning “authorization”
Connectivity and authentication have become increasingly commoditized. Most organizations can point to mature tooling, common best practices and a set of controls that are at least defensible.
Every era has its “worked great” tech. Then the environment changes.
If “governing privileged access” still means vaulting static credentials and shared jump-host accounts, you’re solving yesterday’s problem with yesterday’s tools.
When Neha and Kelsey said the quiet part out loud about privileged access
Agentic systems are accelerating everything. They increase the number of access paths, expand the impact of bad permissions and highlight the limits of tools built for manual control.
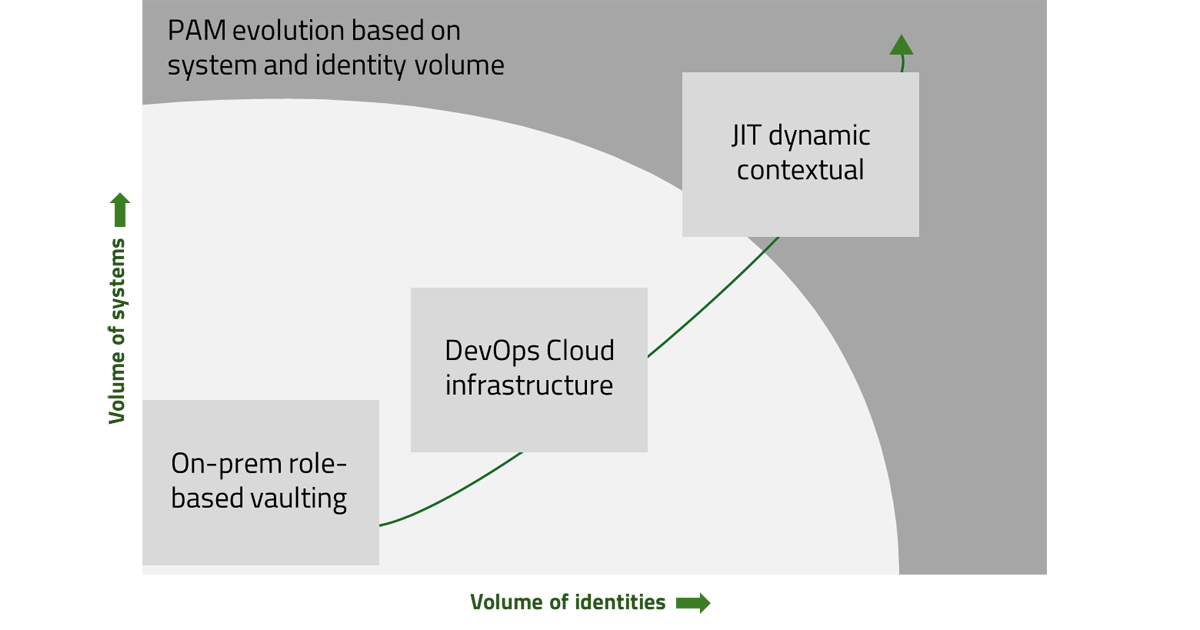
Why PAM Needs to Evolve
Modern-PAM needs to support more systems, more accounts, a hybrid deployment landscape and have the functionality available to a broader array of integrating technologies via modular, composable and API-first capabilities.
The rise of non-human identities and the future of PAM
Learn how security teams can evolve identity programs to manage risk, reduce exposure paths, and prepare for the next wave of AI-driven access.
Why cloud-native demands an API-led approach to PAM
Learn why vaults and jump servers can’t keep up, and how an API-led model delivers just-in-time access, automates least privilege, and strengthens security without slowing developers down.
Ten things to understand when using agentic AI applications
How security, identity, and governance practices must evolve for autonomous software agents Agentic AI applications — from copilots to infrastructure automation bots — are no longer passive assistants. They’re autonomous software actors executing real-world actions:...
Non-Human Identities (NHIs) vs. Machine Identities: Key Differences & Security Best Practices
Discover the key differences between Non-Human Identities (NHIs) and machine identities. Learn best practices to secure service accounts, API keys, and cloud assets.