Securing access for agents and users in privileged environments.
Get P0 AuthZ Control Plane™ for runtime policy enforcement that prevents privilege abuse before it happens.
Zero Standing Privilege by design.
For AI agents
AI agents request runtime access through real-time MCP tool execution workflows.

For users
Human users request fine-grained, ephemeral access through automated approval workflows.
For machines
Non-human identities (NHIs) request programmatic access through platform integrations.
Trusted by security teams, loved by developers.
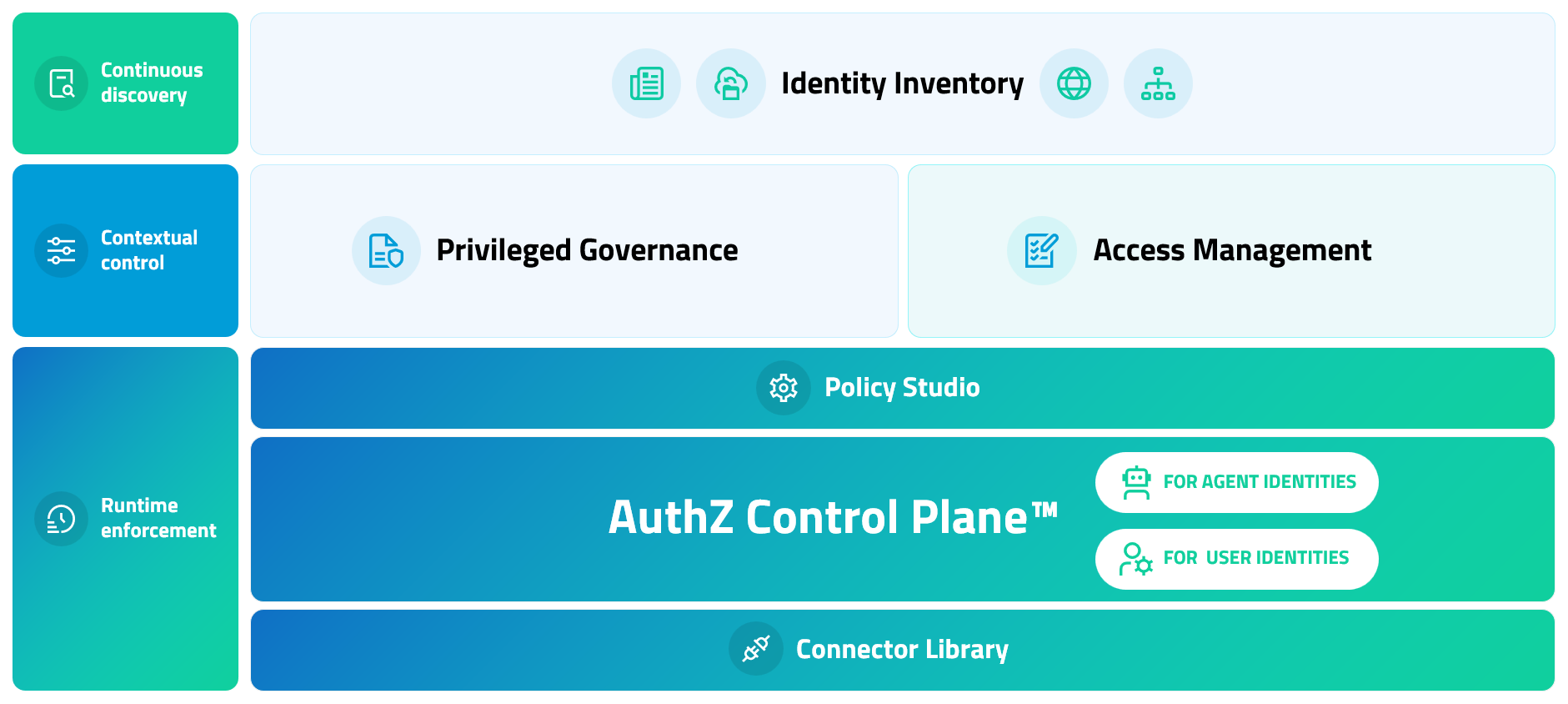
The AuthZ Control Plane™

Dynamic access management
Access when it’s needed. Gone when it’s not.
Authorize ephemeral, scoped access at runtime with context-based authorization that minimizes the identity attack surface.
Continuous privilege governance
Control that holds up under audit.
Govern privilege centrally from discovery to audit with dynamic policy evaluation and on-demand logs that simplifies evidence gathering.


Embedded user workflows
Security that doesn't get in the way.
Embed directly into existing workflows, creating a simple, predictable access experience that developers actually adopt.
Every identity, every permission, everywhere.
Native APIs auto-discover sensitive resources so no privilege goes undetected as environments scale. P0’s agentless architecture eliminates infrastructure overhead, minimizing compute costs and accelerates time-to-ZSP.
Agentic platforms
Amazon Bedrock, Claude, Google Vertex, Microsoft Foundry
Cloud
Amazon Web Services, Google Cloud, Azure, Oracle Cloud Infrastructure
Servers
Virtual machines and on-prem servers with JIT SSH and RDP
Data
PostgreSQL, Amazon RDS, Snowflake and more
All integrations
Kubernetes, code repositories, agentic platforms and more
Modern identity management
Runtime access control for agents and users.
| Legacy access control | |
|---|---|
|
|
|
|
|
|
|
|
Let’s change the way you manage privilege.
See how to extend PAM across hybrid and multi-cloud environments with unified access control for human, non-human, and agentic identities.
Guides, how-tos and best practices.
From real-world customer stories to expert insights and product updates — everything you need to research and evaluate cloud identity.