Blog
Things I’ve learned about early-stage hiring: stop borrowing big-company process too early
I see a pattern in early-stage companies that is easy to miss because it looks like maturity. Teams borrow processes that work later, when an organization is larger and roles are more specialized, and they apply them far too early.
No results found.

4 mins
By shifting toward a model of Zero Standing Privileges and implementing just-enough and Just-in-Time access for AI-driven workflows, security teams can empower their developers without turning their most productive tools into their greatest identity risks.

3 mins
Connectivity and authentication have become increasingly commoditized. Most organizations can point to mature tooling, common best practices and a set of controls that are at least defensible.

3 mins
If “governing privileged access” still means vaulting static credentials and shared jump-host accounts, you’re solving yesterday’s problem with yesterday’s tools.
3 mins
OAuth scopes solve an important part of the authorization puzzle: delegated capability. But they are only one piece. To do MCP authorization properly, you need scopes for the big picture and server-side RBAC for least-privilege enforcement.

3 mins
The ServiceNow breach is a wake-up call. As we deploy more autonomous agents with access to critical business systems, we need authorization architectures designed specifically for the agentic paradigm not retrofitted from traditional security models.

5 mins
Azure AI Studio and Azure OpenAI offer transformative capabilities, but their integration into the Azure ecosystem brings unique identity security considerations.
8 mins
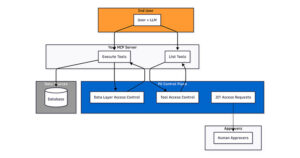
The P0 Authz Control Plane for Agents lets developer and security teams control access for agentic applications that connect to internal data sources, such as a Postgres, Snowflake, Mongo database through a chat interface.

6 mins
Recently, I wrote about the governance challenges and risks associated with Amazon Bedrock and today I’ll explore how the same principles apply to Google Vertex.

3 mins
Agentic systems are accelerating everything. They increase the number of access paths, expand the impact of bad permissions and highlight the limits of tools built for manual control.

6 mins
This is the final of a three-part series taking a look at modern privileged access management and how its evolution to the protection of more systems and more identities leads to both security and productivity improvements.

5 mins
AI agents are increasingly playing a part in how modern developer teams build, automate, and scale.

3 mins
Today’s privileged access challenges demand a shift from static, siloed controls to identity-centric, Just-in-Time (JIT) models that improve security while accelerating deployment and engineering workflows.
No results found.