Blog

Anthropic’s Claude Enterprise
By shifting toward a model of Zero Standing Privileges and implementing just-enough and Just-in-Time access for AI-driven workflows, security teams can empower their developers without turning their most productive tools into their greatest identity risks.
No results found.

4 mins
Broken access control has topped the OWASP Top 10 again — exposing the limits of traditional IAM. Learn why it persists in hybrid and multi-cloud environments and how continuous authorization governance helps close the gap.
5 mins
Generative AI enablers like Amazon Bedrock unlock the innovation potential of AI across the enterprises, but they also significantly expand the identity attack surface.
2 mins
Generative AI has fully entered the enterprise mainstream and platforms like Amazon Bedrock allow organisations to build and scale AI use cases with Foundational Models

2 mins
To wrap up our five-part series on Non-Human Identity (NHI) Governance, we’re sharing a practical self-assessment framework to help teams pinpoint where they stand on the Modern Access Management Maturity Curve.

3 mins
In Part 4 of our Non-Human Identity (NHI) Governance series, Kelsey Brazill explains why this blind spot persists, and what good governance really looks like when extended to machines.
5 mins
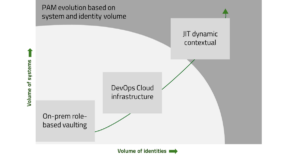
Modern-PAM needs to support more systems, more accounts, a hybrid deployment landscape and have the functionality available to a broader array of integrating technologies via modular, composable and API-first capabilities.

6 mins
In Part 3 of our Non-Human Identity (NHI) Governance series, Kelsey Brazill breaks down why vaulting isn’t enough, what true governance looks like, and how to move from static credentials to ephemeral, just-in-time access.

3 mins
Learn why vaults and jump servers can’t keep up, and how an API-led model delivers just-in-time access, automates least privilege, and strengthens security without slowing developers down.

3 mins
Learn how security teams can evolve identity programs to manage risk, reduce exposure paths, and prepare for the next wave of AI-driven access.

5 mins
In Part 2 of our Non-Human Identity (NHI) Governance series, Kelsey Brazill explores what happens when machine access goes ungoverned AND how to fix it.

4 mins
In Part 1 of our Non-Human Identity (NHI) Governance series, Kelsey Brazill exposes the cloud’s most overlooked attack surface - machine identities - and explains why traditional IAM tools can’t keep up.
How security, identity, and governance practices must evolve for autonomous software agents Agentic AI ...
No results found.