Partnership brings together identity-based connectivity and modern authorization to help organizations reduce ...
Access management

Access to sensitive data slows teams down or gets over-granted to keep things moving. See how Divvy replaced legacy PAM with faster, just-in-time access and cleaner control.
Static SSH keys and shared access seem fine until they turn into risk and audit headaches. See how to move to short-lived, identity-based access that’s easier to manage.

Watch how P0 syncs ServiceNow tickets with real-time access provisioning for seamless and auditable AWS access.

Access workflows have changed, but security still runs on old models that can’t keep up. This API-led approach removes static keys and delivers just-in-time access without slowing teams down.

How to gain visibility into all human + NHI, securing JIT access, and automating access review through dev-friendly workflows.
3 mins
If “governing privileged access” still means vaulting static credentials and shared jump-host accounts, you’re solving yesterday’s problem with yesterday’s tools.

Broad access to Kubernetes clusters creates hidden risk. See how to replace it with least-privilege, short-lived access using fine-grained controls.
Legacy vault workflows create standing access and blind spots. This guide shows how to evaluate modern PAM with just-in-time provisioning, continuous discovery and machine access governance.
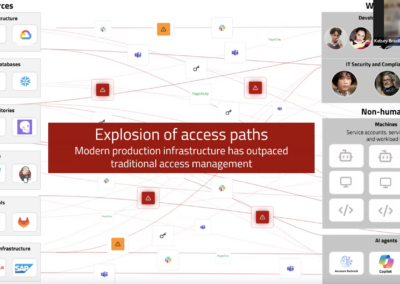
New infrastructure and identities are outpacing legacy security models. This session gives a first-principles framework to rethink identity security and plan next steps.
Static SSH keys and jump hosts slow teams and add risk. See how identity-native, short-lived access secures servers while keeping developer workflows fast and consistent.
See how Dev/Eng teams are moving faster with real-time access workflows.
No results found.