Access doesn’t break all at once, it drifts as permissions pile up across cloud, code and pipelines. See where risks hide and how to move to just-in-time access.
Identity security
Audits expose a hard truth: teams can’t prove who had access, when or why. Learn how to replace standing privilege with JIT access and audit-ready evidence.

4 mins
By shifting toward a model of Zero Standing Privileges and implementing just-enough and Just-in-Time access for AI-driven workflows, security teams can empower their developers without turning their most productive tools into their greatest identity risks.

Static SSH keys and shared access seem fine until they turn into risk and audit headaches. See how to move to short-lived, identity-based access that’s easier to manage.

How P0 identifies unused permissions in GCP, use Access Graph and Policy Studio, to fix misconfigurations, automate approvals, and tie all actions to a user’s identity.

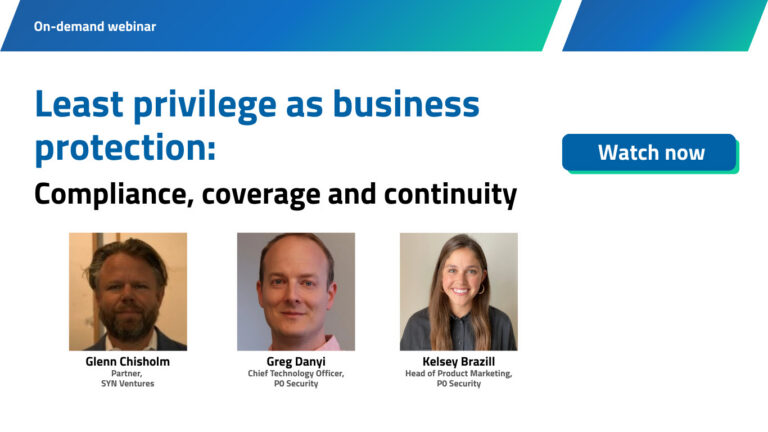
How to gain visibility into all human + NHI, securing JIT access, and automating access review through dev-friendly workflows.

Access workflows have changed, but security still runs on old models that can’t keep up. This API-led approach removes static keys and delivers just-in-time access without slowing teams down.
NHIs power cloud, CI/CD and Kubernetes but create a fast-growing attack surface. Learn how to control them with just-enough, just-in-time access, monitoring and lifecycle governance.

Vault-centric PAM breaks in modern environments and adds risk and drag. This guide shows what to require instead, with identity-native controls and just-in-time access across all identities.

Watch how P0 syncs ServiceNow tickets with real-time access provisioning for seamless and auditable AWS access.

Non-human identities run with persistent permissions and expand your attack surface. Learn how to replace just-in-case access with just-enough, just-in-time controls and real monitoring.

IAM, IGA and PAM struggle with today’s complex identity sprawl. This interview shows why they break and how teams can rethink identity security for modern environments.
No results found.