Platform | Technology
The P0 AuthZ Control Plane™
Replace standing privilege and static credentials with runtime authrozation control that's tailor made for agile production environments. Discover, govern and enforce least-privileged access without slowing teams down.
Have you outgrown traditional access management?
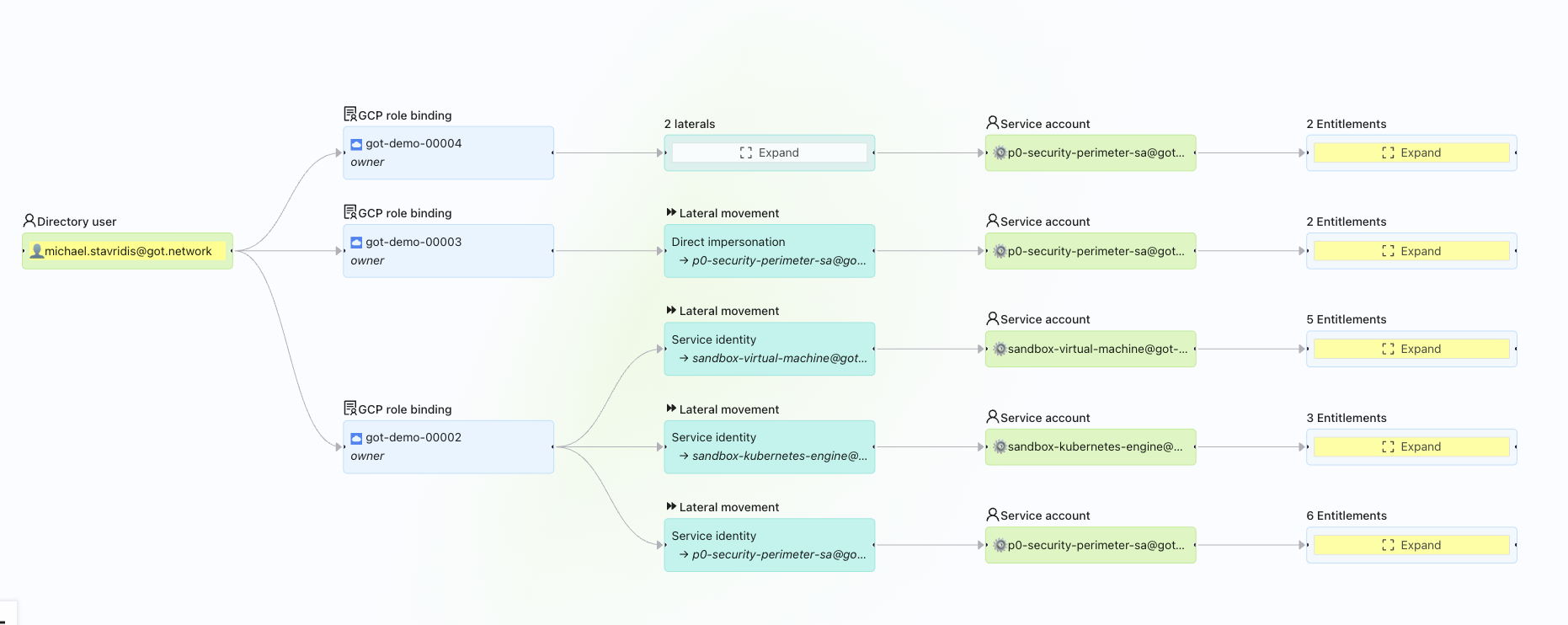
As the traditional network perimeter dissolves and identity becomes the new frontier, privilege has spread to include new identity types and a proliferation of access paths into sensitive systems. Modern production environments are more complex and expansive than ever before. Sensitive systems are now accessed by developers, service accounts, ephemeral workloads and AI agents across vastly distributed environments and dynamic application-layer APIs.
Trying to solve today’s reality by retrofitting solutions built for the past has left organizations grappling with static credentials, shared accounts and an unacceptable amount of standing privilege risk.
Control every user, AI agent and workload
P0 Security manages the entire privilege lifecycle in order to deliver secure and auditable access at developer speed. As the AuthZ Control Plane™ for modern production environments, P0 centralizes governance and enforces just-enough privilege and just-in-time access across every sensitive system.
Zero standing privilege. Zero added friction. Because secure production access is Priority Zero™.
Our mission
Keep the business secure and teams running fast so they can protect what matters, reduce the unknowns and continue to innovate.
Identity-first authorization
Persistent identity. Ephemeral access.
Delivering ZSP at enterprise scale requires a unified control plane that spans multi-cloud IAM, Kubernetes, SaaS systems, and agentic AI platforms. Enterprises need security that keeps pace with the speed, sprawl, and flexibility of modern times.
Authorization is the layer where access has to be controled in order to ensure it is least-privileged, auditable and as dynamic and scalable as the environments it aims to secure.
By decoupling authentication and authorization, teams maintain persistent verified identities and introduce dynamic access control, eliminating the risk of shared accounts and static credentials and simplifying access workflows for everyone involved.
From discovery to control in minutes.
P0’s lightweight architecture pulls all identity related metadata across sensitive systems into a single source of truth. This provides the context needed to discover, govern and enforce policy-driven control across your entire production stack.

Remove governance overhead and audit complexity
Tie all user, machine and agentic access back to the IdP for complete privilege visibility, contextual controls and user-level audit trails.

Minimize static credentials and shared accounts
Enforce least-privileged, just-in-time access natively across systems to remove persistent access and reduce the identity attack surface.
Simplify operations and developer workflows
Deliver a consistent, low-friction experience across multi-cloud and hybrid environments that integrates seamlessly with existing workflows.

"Exceeded all my expectations."
"Temporary access used to be slow, manual, and buried in IAM group sprawl. With P0, we grant secure, fine-grained permissions in real time through Slack or CLI, using workflows that match how our engineers actually work. It’s fast, flexible, and lets us move lean and stay compliant without the usual overhead."
Johnny Chen
DevSecOps Engineer and InfoSec Manager, Finix
Dynamic access management
Access when it's needed. Gone when it's not.
Enforce ephemeral, scoped access exactly when it’s needed with context-based authorization that minimizes the identity attack surface.
Continuous privilege governance
Control that holds up under audit.
Centrally govern privilege from discovery to audit with dynamic policy evaluation and on-demand logs that make incident investigations and audit prep easier than ever before.
Guides, how-to's and best practices.
From real-world customer stories to expert insights and product updates...everything you need to research and evaluate cloud identity.


