Outcomes | Modernization
Developer velocity
Give developers the access they need, exactly when they need it without any left over privilege or added friction.

Security only works when it works with the business, not against it.
Security teams and development teams have always had an uncomfortable tradeoff: lock everything down and frustrate your engineers, or give broad access and accept the risk. That tension doesn't have to be normalized. P0 Security replaces it with just-in-time access workflows that are fast enough for developers to actually use. Requests via Slack, CLI, or GitHub, approvals in minutes, access that expires automatically. Security controls stay intact. So does developer velocity.
The problem
Fear of breakage outweighs security.
When access provisioning is slow or cumbersome, developers find workarounds. Persistent admin access gets requested and never revoked. Shared credentials circulate across teams. Service accounts accumulate permissions that nobody reviews. The longer access takes to provision, the more pressure there is to just grant it permanently. That is where standing privilege starts to compound.
Slow provisioning pushes engineers toward risky permanent access
Shared credentials kill auditability and outlast the projects that created them
Security friction drives developers to ungoverned workarounds
The solution
Secure paths get adopted when they’re simple.
P0 Security delivers just-in-time access through the channels developers already use via Slack, Teams, CLI, email or the web. Requests take seconds to submit and minutes to approve. Every grant is time-limited, identity bound, least-privilege, and fully auditable. Developers get what they need without friction. Security teams get visibility and control without becoming a bottleneck.
Self-service, least-privileged access without tickets or manual provisioning
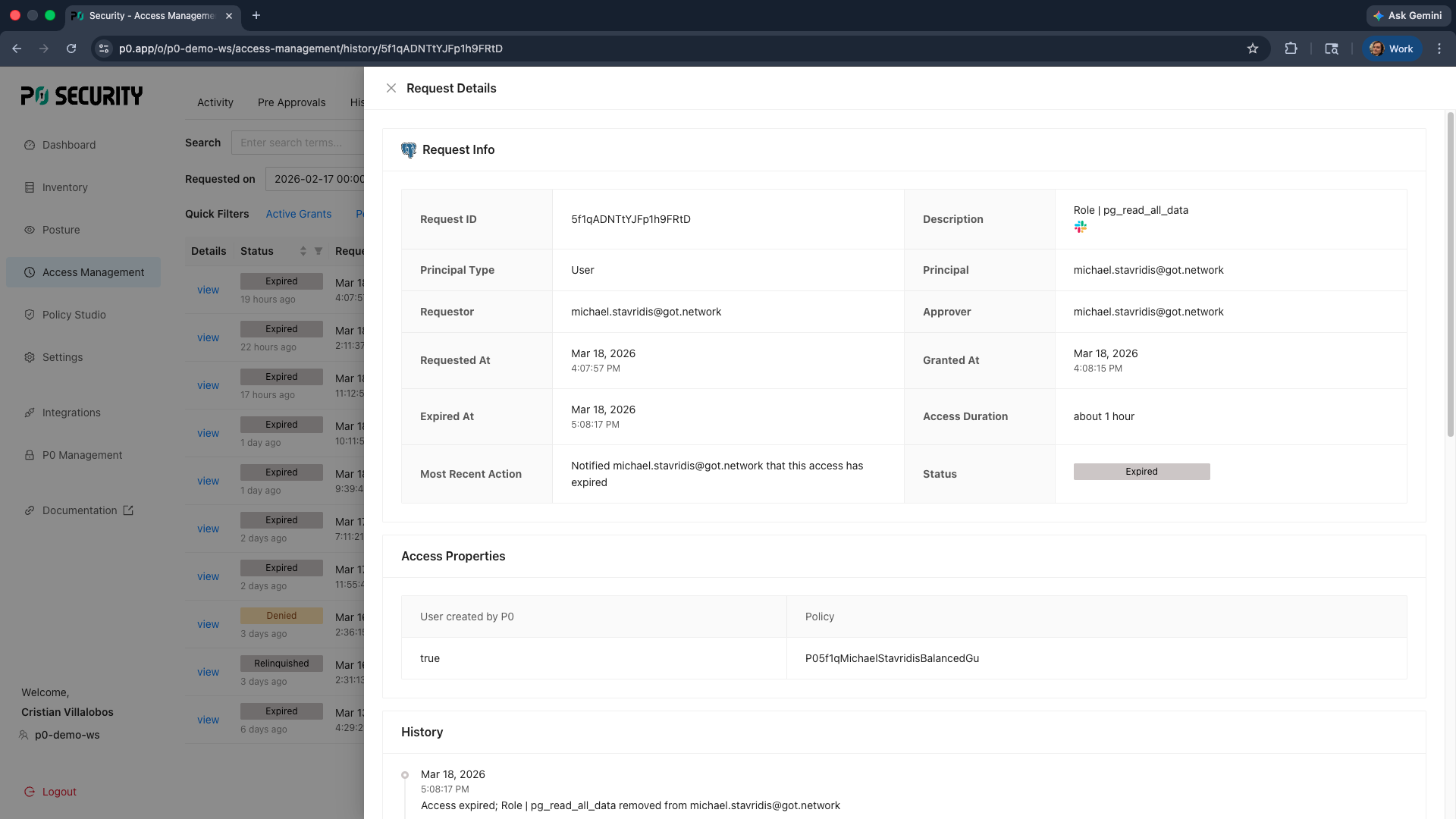
Auto-expiring access eliminates persistent permissions nobody remembers granting
Security controls embedded in developer workflows, not layered on top
Capability highlights
Slack and CLI access requests
Developers request production access directly from Slack or the command line. Requests include context, approvals route to the right people, and access is provisioned automatically.
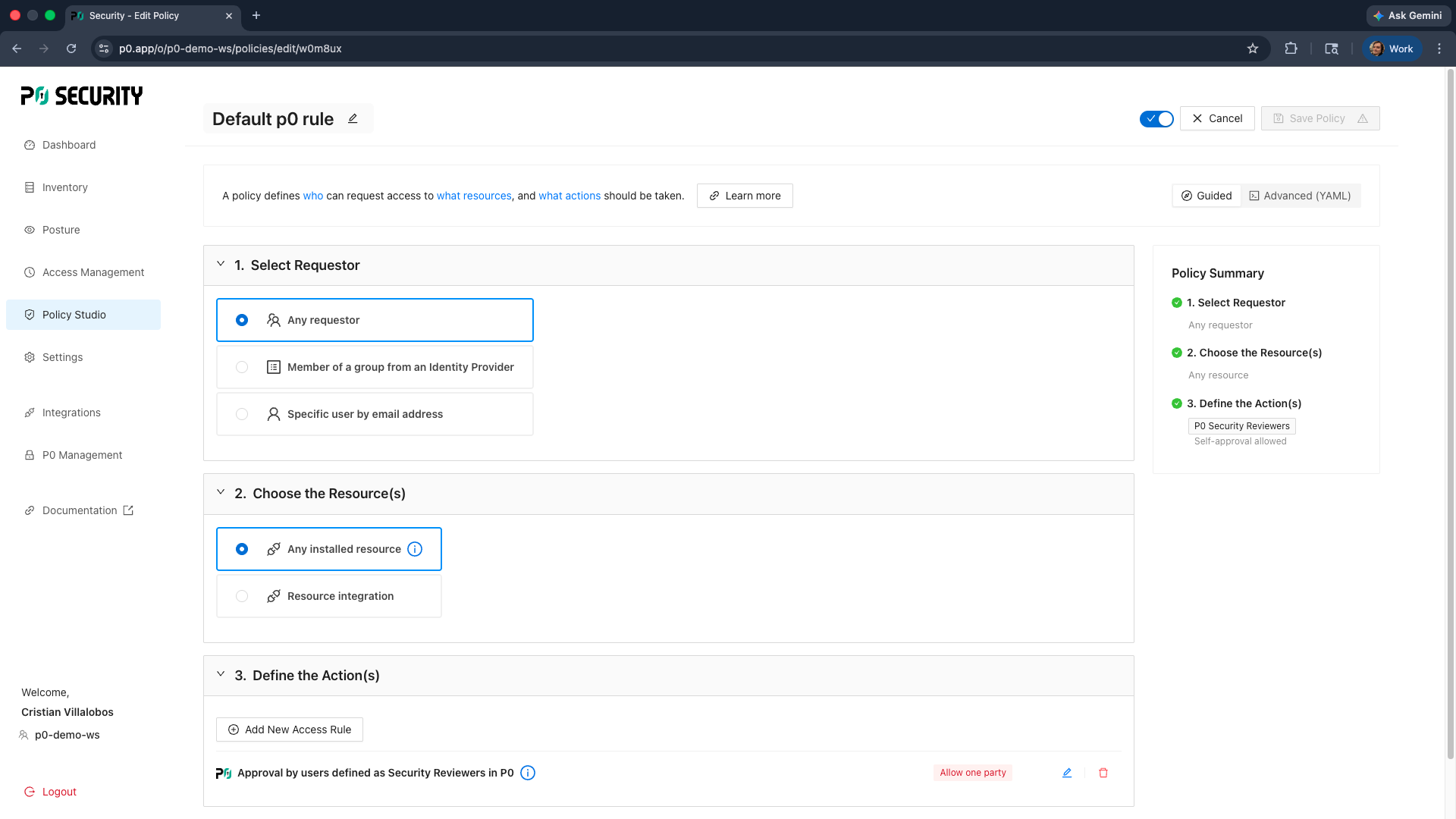
Policy-based approval automation
Define approval rules so low-risk access requests are auto-approved and only sensitive requests require human review. Reduce security team overhead without relaxing controls.
Time-bound, scoped grants
Every access grant is scoped to the minimum required permissions and expires automatically. Nothing persists beyond what was requested and approved.