Welcome IDAC members
Learn how P0 Security delivers the next-gen PAM solution
P0 Security helps security and IT teams manage and govern privileged access across all human and non-human identities—securing cloud and hybrid environments at scale.

Next-Gen PAM for users, NHIs and agentic AI
In this sponsor spotlight episode, Jim and Jeff are joined by Shashwat Sehgal, CEO and founder of P0 Security, to discuss the evolving challenges of privileged access management in modern, cloud-native environments. Shashwat explains how traditional PAM solutions often create friction for developers, leading to over-provisioning and security risks, and how P0 is tackling this problem with a developer-first, just in time (JIT) access model.
The conversation covers the core problems with developer productivity, how P0's technology provides deep visibility and control without proxies or bastions, the "Priority Zero" philosophy, and how a JIT approach simplifies audits and compliance. They also discuss the competitive landscape and what sets P0 Security apart from traditional and open-source solutions.
Technical differentiation
- Developer-centric: Offers frictionless access via CLI commands or Slack-based approvals—no ticketing required.
- Agentless and proxy-less: Native integrations with cloud IAM systems (e.g., AWS IAM/STS, GCP IAM, GitHub). No jump hosts or bastions.
- Unified identity model: Supports users, service accounts, NHIs and AI agents under a single access policy engine.
- Rapid deployment: Deploys in hours, not weeks. No infrastructure to maintain.
- Extensible: Flexible APIs and SDK that can extend P0’s governance capabilities to third party apps
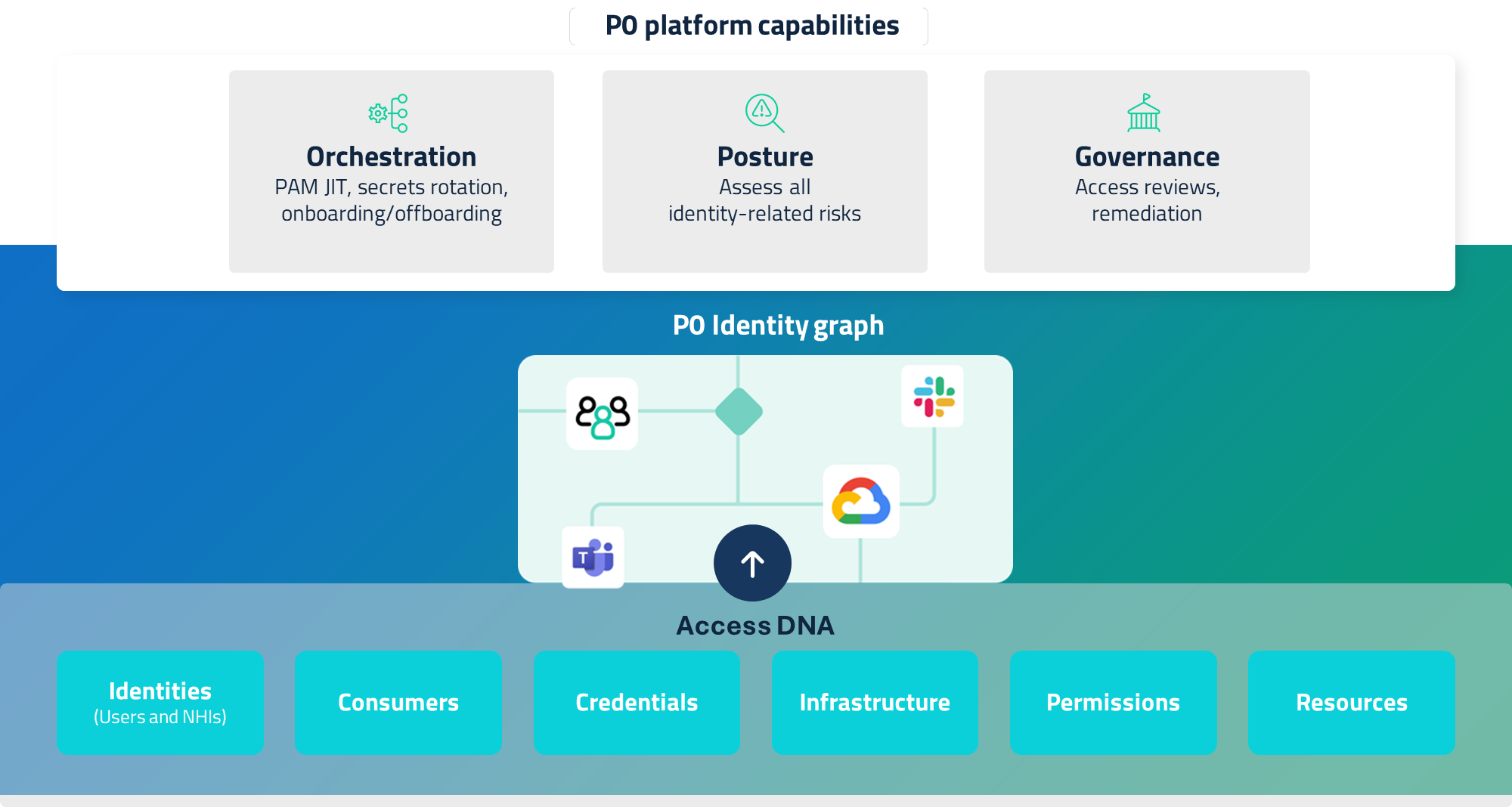
Core capabilities
- Orchestration: Provisions short-lived, just-in-time, least-privileged access for users, and scoped permissions for NHIs, all via native IAM APIs, with a best-in-class developer experience.
- Posture analysis: Continuously evaluates blast radius, usage patterns, stale credentials, and excessive privileges. Surfaces the most exploitable risks across clouds.
- Governance: Enforces policy-as-code using the identity graph, automates access reviews, and integrates with frameworks like SOC 2 and ISO 27001 for full audit readiness.
Value by role
Security teams
Gain visibility into who has access, when, and why—plus automated least-privilege enforcement.
Developers
Get scoped, time-bound access from inside familiar tools—no extra friction.
Platform engineers
Replace brittle scripts with scalable access-as-code policies.
CISOs
Eliminate standing access and measure risk reduction across identity types.
Compliance teams
Automate evidence collection, approval trails, and entitlement reviews.
Resources
Connect with Shashwat: https://www.linkedin.com/in/shashwatsehgal/
Connect with us on LinkedIn: https://www.linkedin.com/company/p0-security/
Jim McDonald: https://www.linkedin.com/in/jimmcdonaldpmp/
Jeff Steadman: https://www.linkedin.com/in/jeffsteadman/
Visit the show on the web at idacpodcast.com