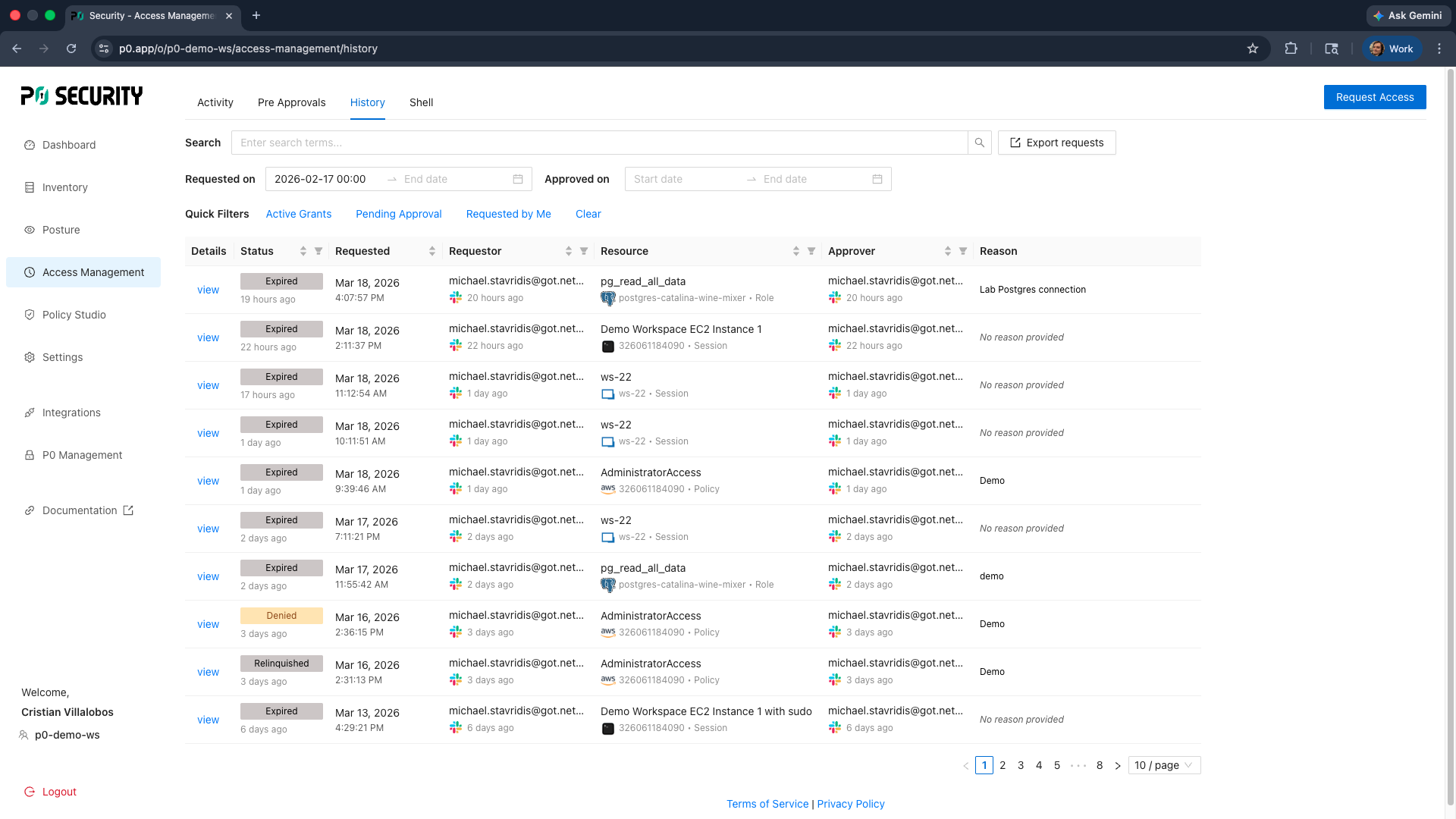
Outcomes | Access Management
Identity-first SSH and RDP access
Replace static SSH keys and RDP credentials with short-lived, identity-verified access to every server in your infrastructure.

Accessing servers should not rely on static credentials or shared accounts.
SSH keys and RDP credentials were designed for connectivity, not governance. Once provisioned, they persist indefinitely; often across role changes, team departures, and infrastructure evolution, with no built-in mechanism for review or revocation. Most organizations have more active server access than they realize, held by more identities than they can track. P0 Security replaces static credentials with short-lived, IdP-tied access that is automatically provisioned and expired, bringing real privilege governance to your most sensitive infrastructure layer.
The problem
Access outlives the task at hand.
SSH keys and RDP credentials have a fundamental design limitation: they do not expire unless you make them. In practice, access granted for a project, an on-call rotation, or a new hire persists long after the reason for it has gone. With the average enterprise managing hundreds or thousands of servers, key sprawl becomes a governance problem at a scale that manual processes cannot address.
SSH keys accumulate from contractors, leavers and repurposed accounts with no lifecycle
Static credentials authenticate without accountability for what happens next
Shared keys and passwords destroy individual accountability and traceability
The solution
Identity-first authorization.
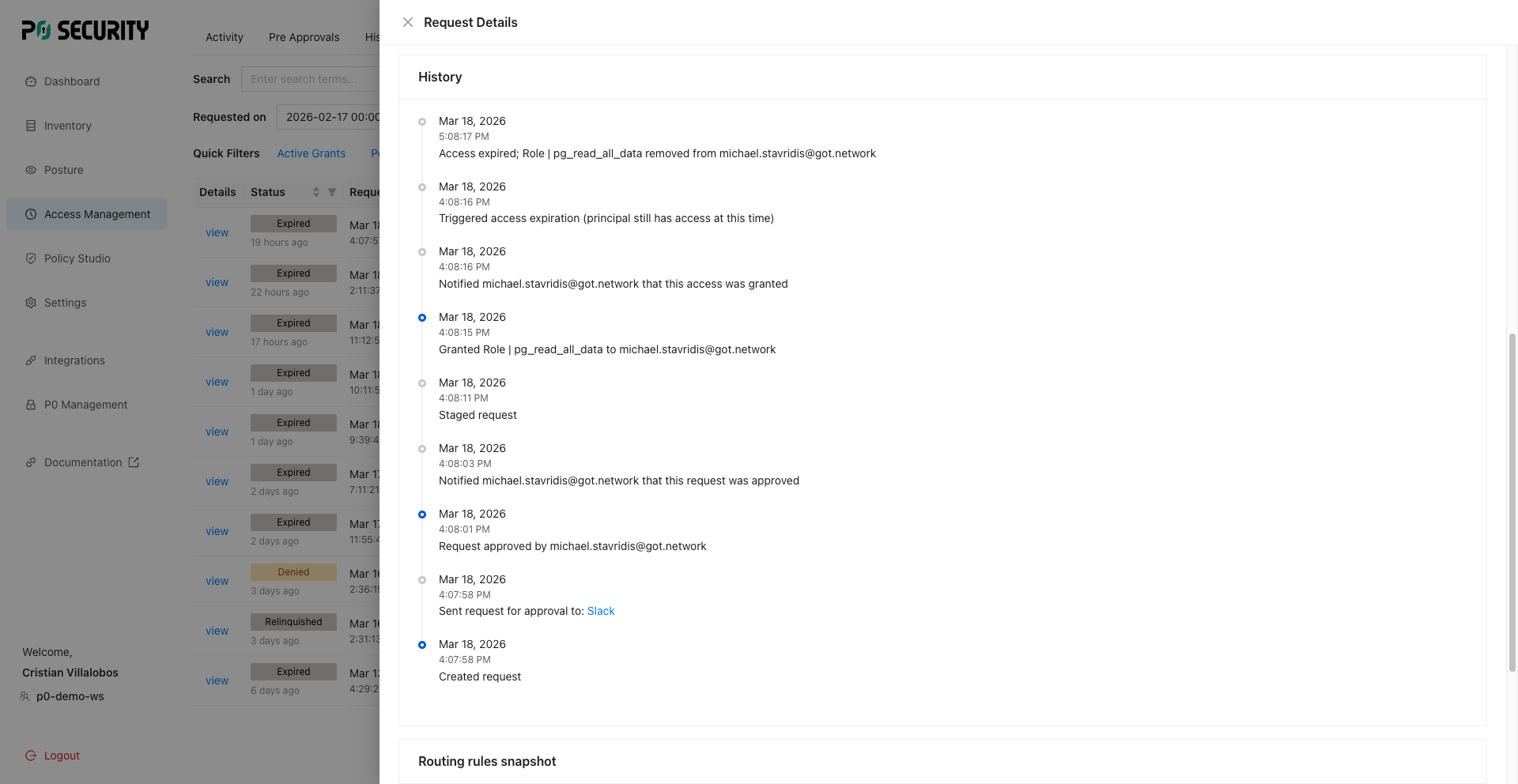
P0 Security replaces static SSH keys and RDP credentials with short-lived, IdP-tied certificates that are issued on demand and expire automatically. Access is authenticated through your existing identity provider; no bastion hosts, no credential vaults, no key distribution infrastructure required. Every session is tied to a named identity, with full audit logs and optional session recording across every server in your infrastructure.
Per-session access replaces persistent keys and expires automatically.
Every session tied to a named identity with full logging
One governed workflow tied to your identity provider across every server
Capability highlights
Just-in-time RDP access to Windows
Short-lived, IdP-tied RDP certificates replace static credentials. Engineers get access when they need it, authenticated through your identity provider, with no bastion host or credential vault required.
Central server access governance
P0 brings the same short-lived, identity-first access model to RDP or SSH sessions, eliminating persistent credentials across servers and virtual machines in your infrastructure.
Session logging and recording
Every SSH and RDP session is logged with full context: who accessed what, when, and from where. Session recording is available for high-sensitivity access events and compliance evidence.