Platform | Technology
For users
Deliver least-privileged access for every developer at runtime Replacing standing privilege with identity-driven, policy-based authorization to production systems.
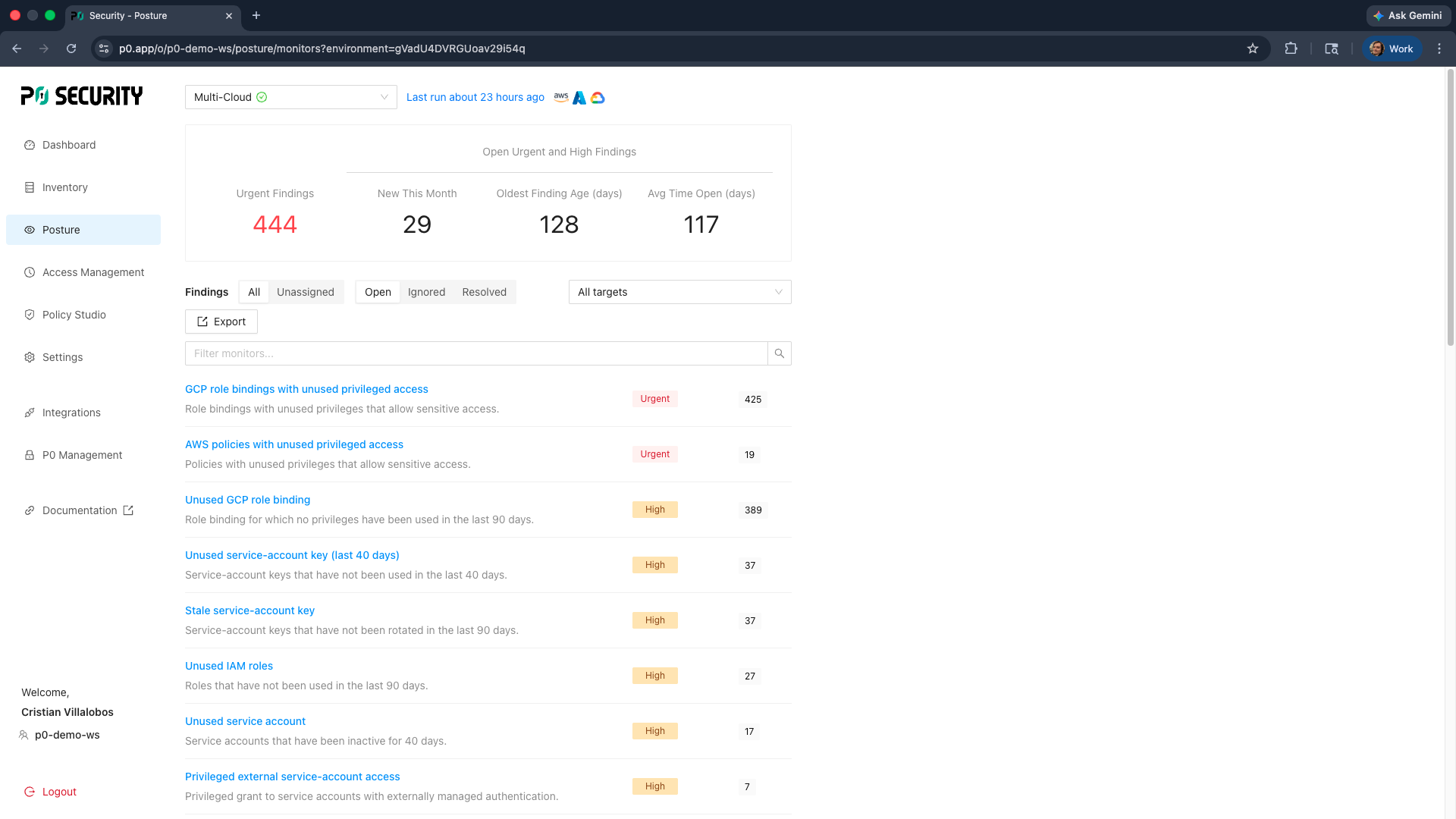
When you don’t know who has access to what or why.
Enterprises are still managing developer access with static credentials, shared accounts and manual approvals that slow teams down and increase risk. Persistent permissions accumulate over time, access reviews fall behind and developers are forced to navigate complex workflows just to get work done. The result is an environment where access is both over-provisioned and operationally painful.
Solution
Keep developers moving, without leaving privilege on the table.
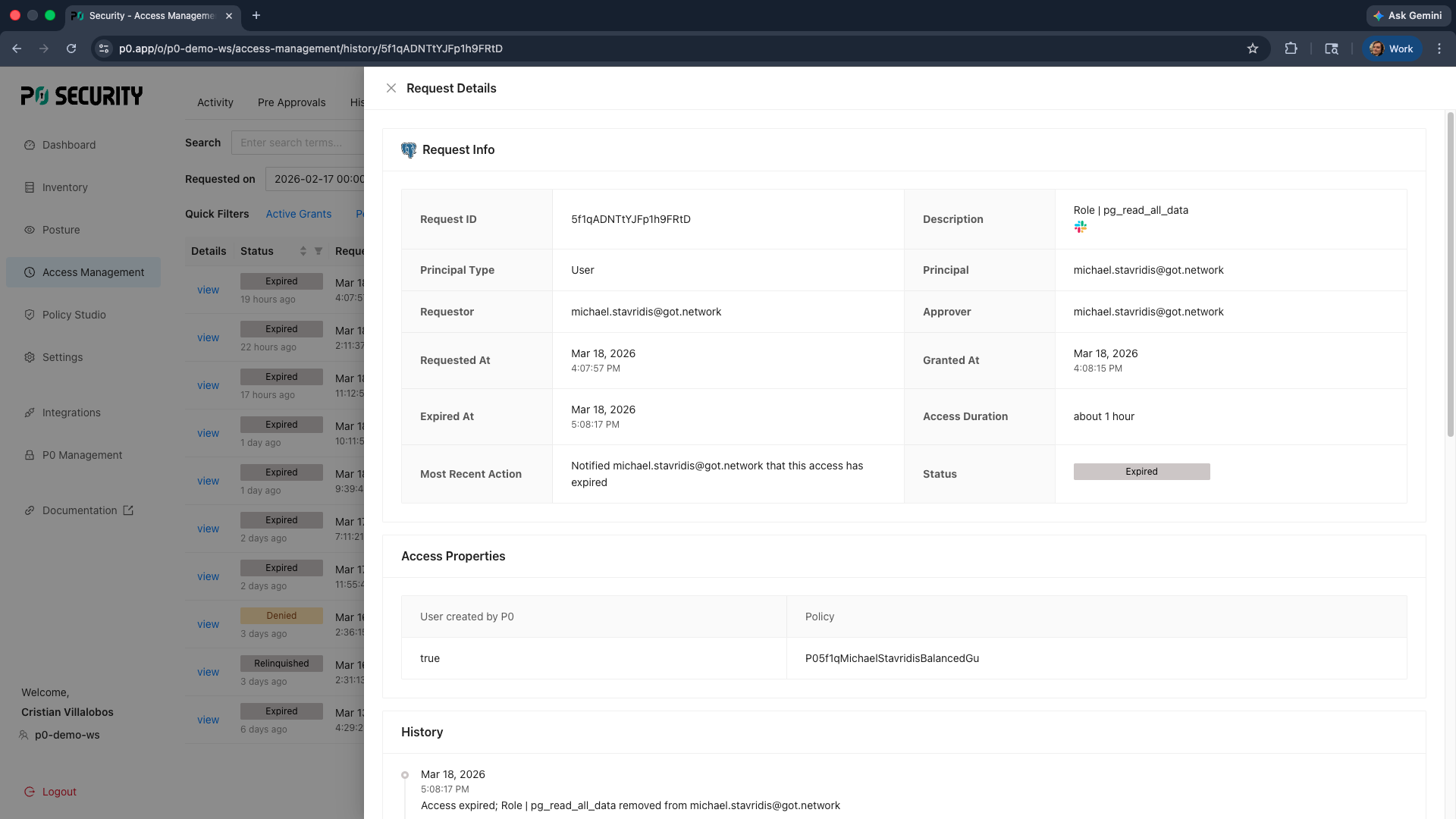
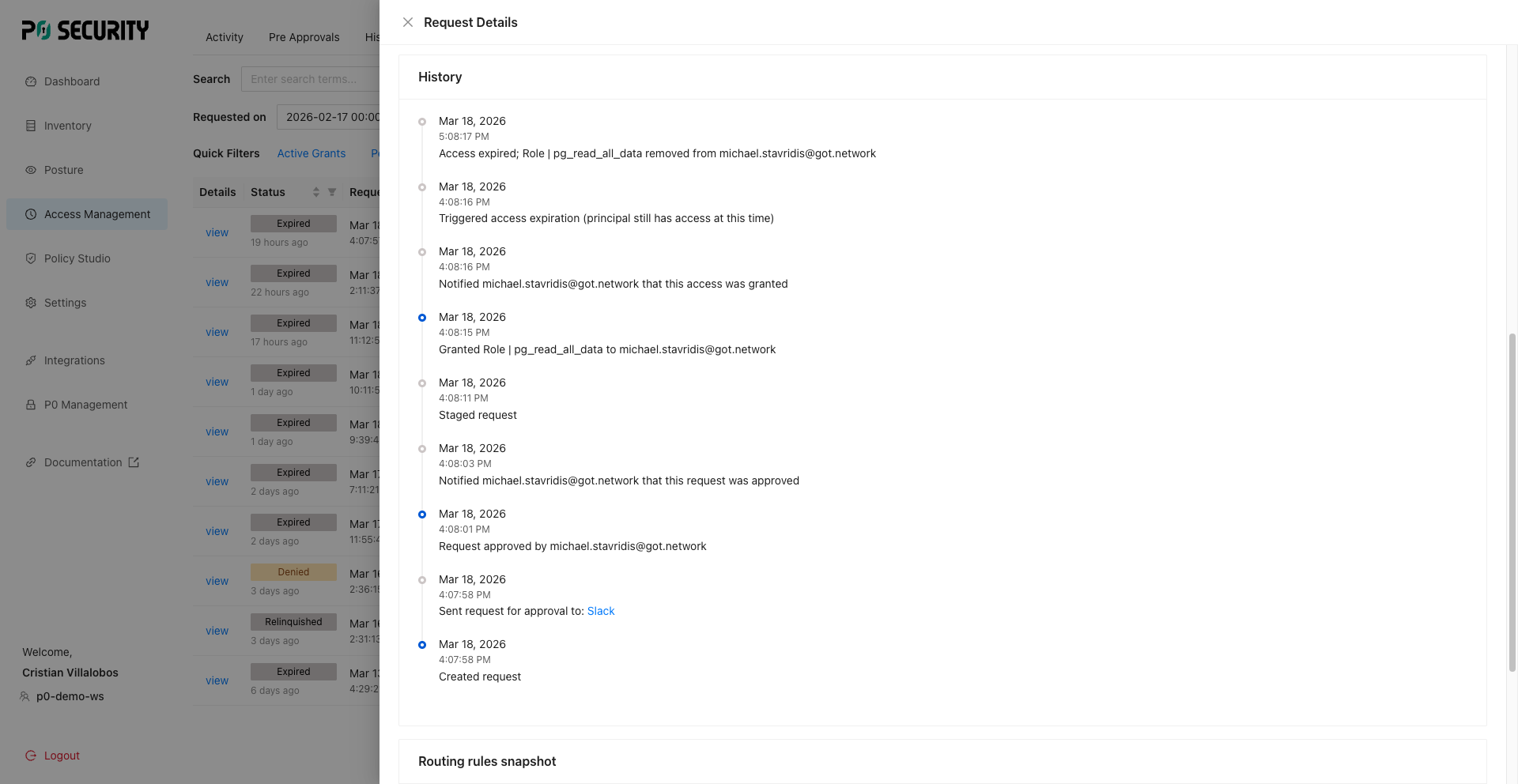
P0 replaces static credentials, shared accounts and manual provisioning with dynamic, policy-driven authorization. Developers request access when they need it, P0 evaluates that request against policy and provisions just-enough privilege, just-in-time. No vaults, no shared keys, no disruption to developer workflows – just fast, auditable access that’s always tied to a verified identity.
Seamless access
When the secure path is simple and predictable, teams adopt it willingly. Usability reinforces strong security rather than competing with it.
Deliver least-privileged, auditable and agile access to ensure adoption.
P0 centralizes how privileged access is requested, approved and enforced across your entire production environment. With runtime authorization controls, P0 eliminates standing privilege and ensures every action is scoped, time-bound and tied to an accountable user identity.

Identity-first authorization
Every session is tied to a verified IdP identity, eliminating shared accounts, static credentials and audit headaches.

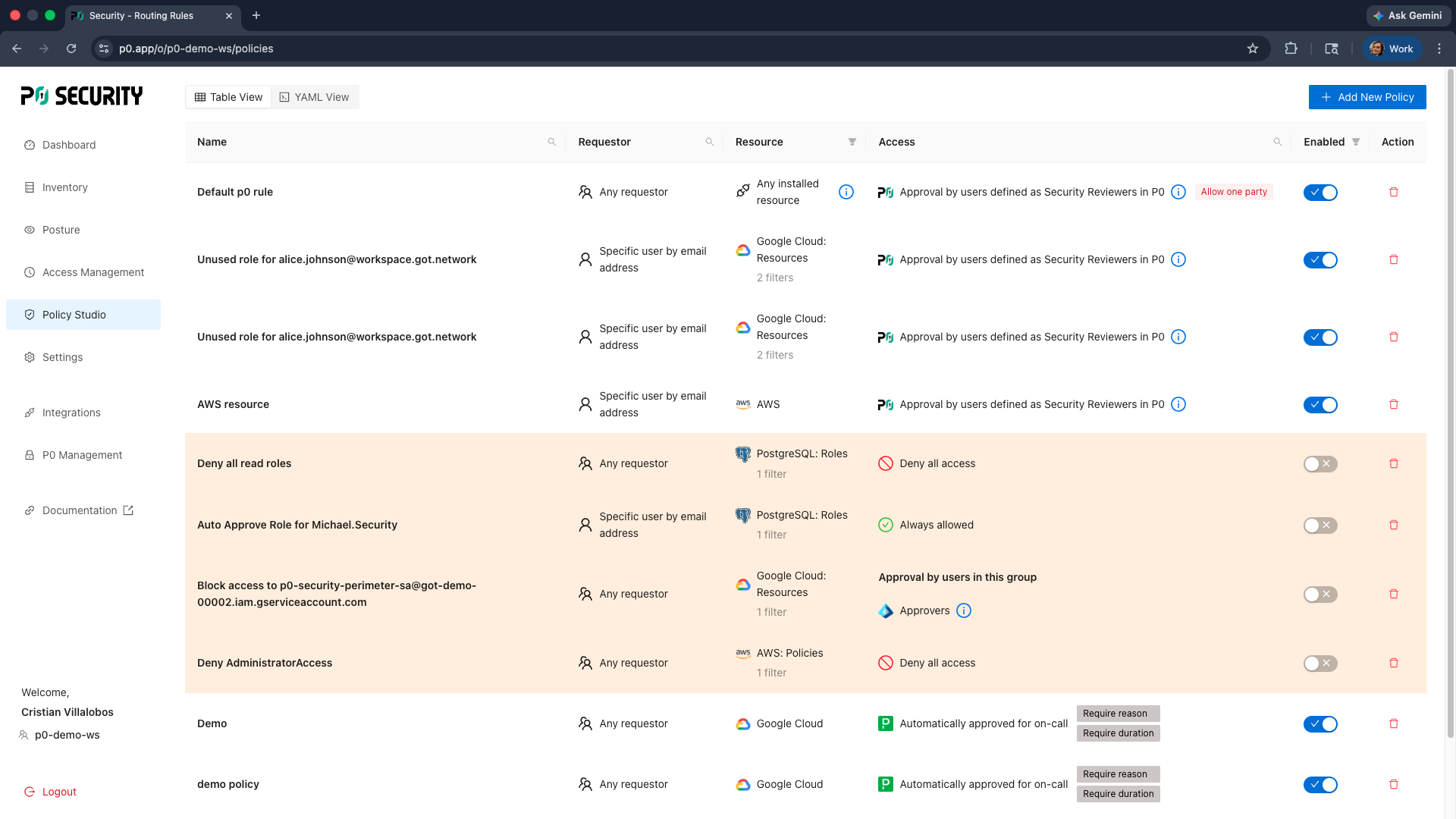
Runtime policy enforcement
Automated approval workflows tailored to your unique risk tolerance and policy for scalable control.
World-class user experience
Gain direct access to native systems without ever having to leave your existing workflows or chatops tooling.

“As leaders in enterprise AI, Resolve AI sees security as a core responsibility. As we transform how engineering teams manage and run production systems with our AI SRE, P0 Security delivers us just-in-time access that’s both secure and easy to use. Its deep coverage of our production environment with continuous audit trails have made P0 our standard for access management, centralizing control and streamlining security reviews.”
Madhu CS
Resolve AI
"P0 Security delivers us just-in-time access that’s both secure and easy to use.”
Guides, how-tos, and best practices.
Categories set for this page currently "IAM" and Identity?" Lorem ipsum dolor sit amet, consectetur adipiscing elit. Donec mattis orci tristique velit finibus ultrices. Curabitur non magna at est rutrum lobortis. Integer posuere pretium sagittis. Morbi rhoncus imperdiet